Purpose
This article explains how to block the installation of 3rd-party password manager extensions in Microsoft Edge and Google Chrome using Microsoft Intune.
Prerequisites
-
Microsoft 365 tenant with Global Administrator or Intune Administrator role
-
Intune licensing (e.g. Intune Plan 1, Microsoft 365 E3/E5, or Business Premium). Note: Microsoft Entra ID alone does not include Intune capabilities
-
Devices must be enrolled in Intune
Instructions
- Sign in to the Microsoft Intune Admin Center
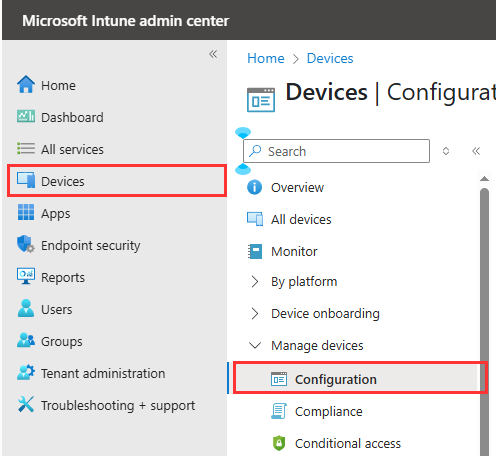
- In the left menu, click on Devices and then click on Configuration under Manage devices
- On the Policy tab, click Create and select New Policy

- Continue with the steps below for each required browser. You’ll need to create a separate policy or profile for every browser you intend to block.
- Configure the following
- For Platform choose Windows 10 and Later
- For Profile Type choose Settings catalog

- Click Create
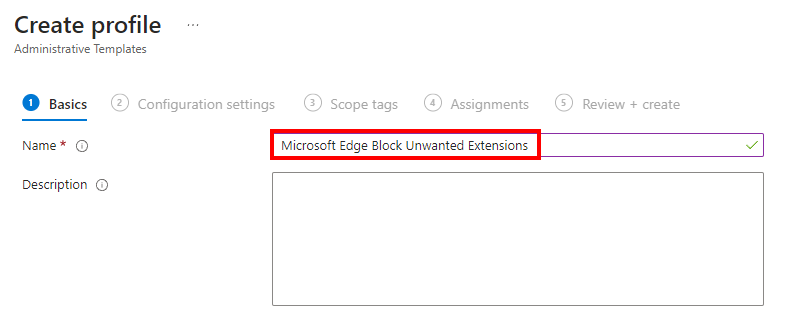
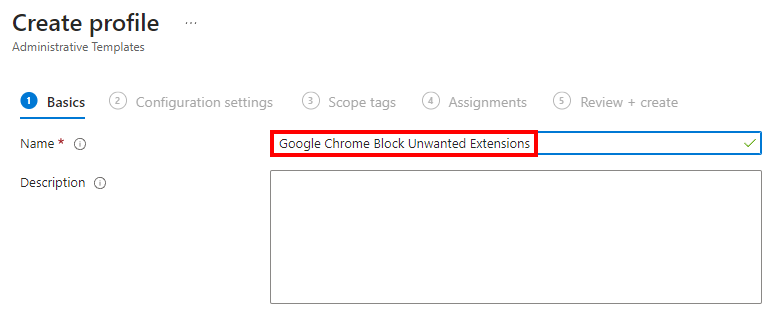
- On Basics setup, set the Name to Microsoft Edge – Block Unwanted Extensions and click Next.
- In the Configuration settings tab, click Add settings.

- Search for Control which extensions cannot be installed and choose Microsoft Edge\Extensions
- In the Setting name tick the box for Control which extensions cannot be installed

- Enable the switch for Control which extensions cannot be installed
- Enter each extension IDs you want to block in the field. Refer to the list of common Edge Password Manager IDs provided below.
Bitwarden: jbkfoedolllekgbhcbcoahefnbanhhlh 1Password: dppgmdbiimibapkepcbdbmkaabgiofem Dashlane: gehmmocbbkpblljhkekmfhjpfbkclbph OneLogin: mpnjdddkcbccdhgahjdcjppglaecajdj Okta: ncoafaeidnkeafiehpkfoeklhajkpgij Keeper: lfochlioelphaglamdcakfjemolpichk Keeper: mpfckamfocjknfipmpjdkkebpnieooca LastPass: bbcinlkgjjkejfdpemiealijmmooekmp
Note: Keeper has published 2 extensions in the Edge Store, requiring both of the above IDs to be used when blocking the extension.
- Click Next.

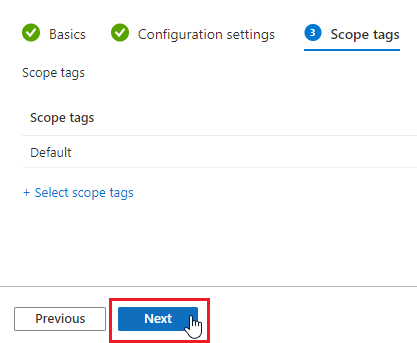
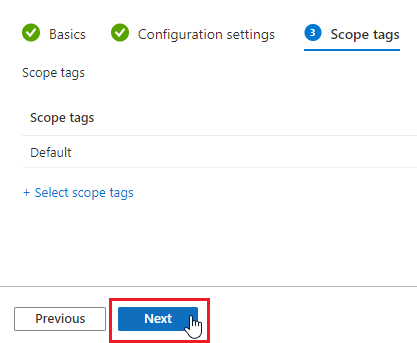
- Leave scope as Default and click Next.
- On the Assignments tab, Click on Add all users and Add all devices.
Note: If you don’t want to deploy the policy to all users, select Add groups and assign it only to the preferred group.
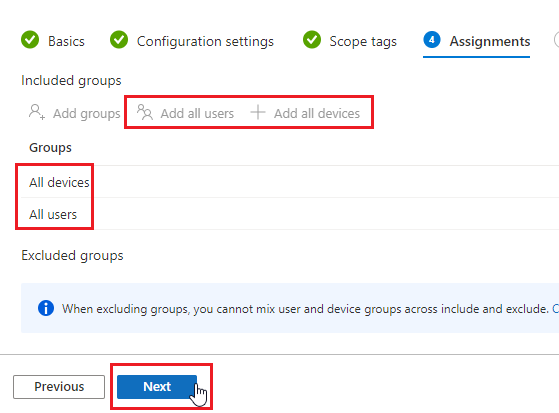
- Click Next.
- Review the settings to ensure the extension IDs are correct.
- Click Create

- The policy will be enforced on targeted devices at their next Intune check-in
- Configure the following
- For Platform choose Windows 10 and Later
- For Profile Type choose Settings catalog
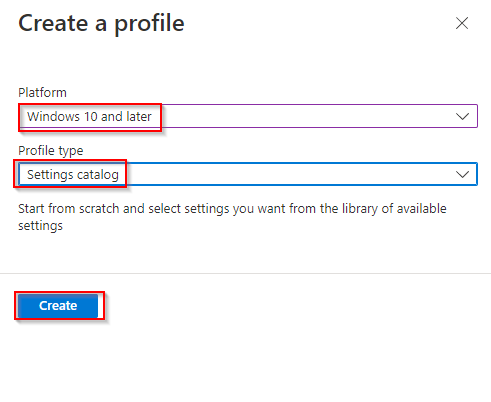
- Click Create
- On Basics setup, set the Name to Google Chrome – Block Unwanted Extensions and click Next.
- In the Configuration settings tab, click Add settings.

-
Search for Chrome and select Google Google Chrome Extensions in the list
- In the Setting name tick the box for Configure extension installation blocklist

- Enable the switch for Configure extension installation blocklist
- Enter each extension IDs you want to block in the field. Refer to the list of Common Chrome Password Manager IDs provided below.
Bitwarden: jbkfoedolllekgbhcbcoahefnbanhhlh 1Password: dppgmdbiimibapkepcbdbmkaabgiofem Dashlane: gehmmocbbkpblljhkekmfhjpfbkclbph OneLogin: mpnjdddkcbccdhgahjdcjppglaecajdj Okta: ncoafaeidnkeafiehpkfoeklhajkpgij Keeper: lfochlioelphaglamdcakfjemolpichk Keeper: mpfckamfocjknfipmpjdkkebpnieooca LastPass: bbcinlkgjjkejfdpemiealijmmooekmp
Note: Keeper has published 2 extensions in the Edge Store, requiring both of the above IDs to be used when blocking the extension.

- Click Next.
- Leave scope as Default and click Next.
- On the Assignments tab, Click on Add all users and Add all devices.
Note: If you don’t want to deploy the policy to all users, select Add groups and assign it only to the preferred group.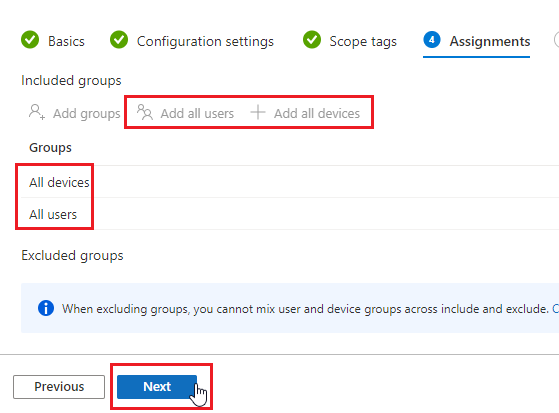
- Click Next.
- Review the settings to ensure the extension IDs are correct.

- Click Create
- The policy will be enforced on targeted devices at their next Intune check-in
