Purpose
This article outlines the steps to configure Microsoft Intune policies to block browsers from saving or remembering user credentials, helping maintain security compliance across managed devices.
Prerequisites
-
Microsoft 365 tenant with Global Administrator or Intune Administrator role
-
Intune licensing (e.g. Intune Plan 1, Microsoft 365 E3/E5, or Business Premium). Note: Microsoft Entra ID alone does not include Intune capabilities
-
Devices must be enrolled in Intune
Instructions
- Sign in to the Microsoft Intune Admin Center
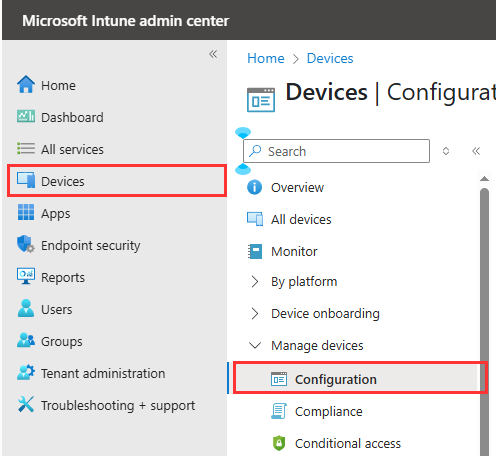
- In the left menu, click on Devices and then click on Configuration under Manage devices
- On the Policy tab, click Create and select New Policy

- Continue with the steps below for each required browser. You’ll need to create a separate policy or profile for every browser you intend to block.
- Configure the following
- For Platform choose Windows 10 and Later
- For Profile Type choose Settings catalog

- Click Create
- Name the Profile to Block Password Saving – Microsoft Edge and click Next.

- In the Configuration settings tab, click Add settings.

- Search for Password Manager
- Choose Microsoft Edge\Password manager and protection
-
In the Setting name, tick the box for Enable saving passwords to the password manager.

-
In the left panel, ensure that the switch for Enable saving passwords to the password manager is set to Disabled. This will prevent users from storing passwords in the browser for improved security.

-
Click Next to continue.
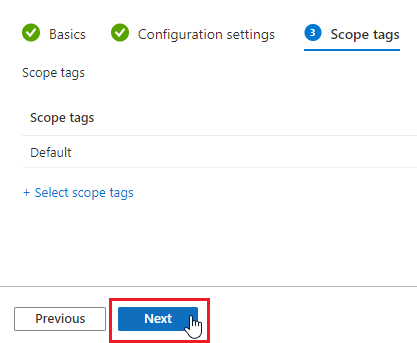
- Leave scope as Default and click Next.
- On the Assignments tab, Click on Add all users and Add all devices. Note: If you don’t want to deploy the policy to all users, select Add groups instead and assign it only to the preferred group.
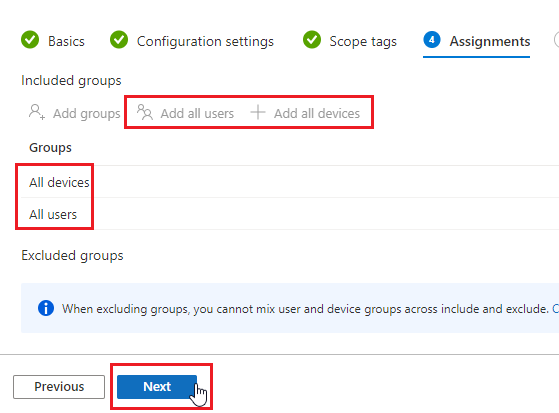
- Click Next.
- Review the settings and ensure password saving option is disabled.

- Click Create
- The policy will be enforced on targeted devices/users at their next Intune check-in
-
- Configure the following
- For Platform choose Windows 10 and Later
- For Profile Type choose Settings catalog

- Click Create
- Name the Profile to Block Password Saving – Google Chrome and click Next

- In the Configuration settings tab, click Add settings.

- Search for Password Manager
- Choose Google Google Chrome Password manager
- In the Setting name, tick the box for Enable saving passwords to the password manager.

- In the left panel, ensure that the switch for Enable saving passwords to the password manager is set to Disabled. This will prevent users from storing passwords in the browser for improved security.

- Click Next to continue.
- Leave scope as Default and click Next.
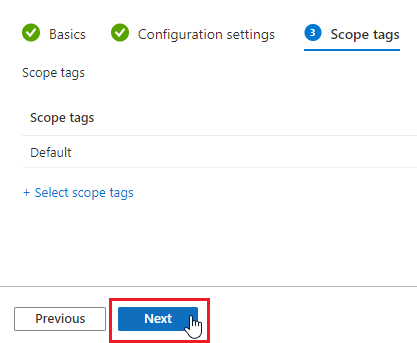
- On the Assignments tab, Click on Add all users and Add all devices. Note: If you don’t want to deploy the policy to all users, select Add groups instead and assign it only to the preferred group.
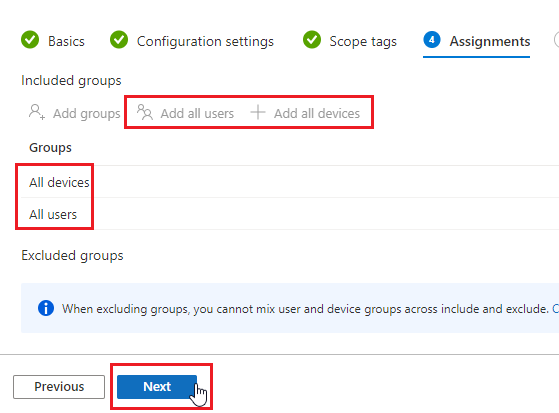
- Click Next.
- Review the settings and ensure password saving option is disabled.

- Click Create
- The policy will be enforced on targeted devices/users at their next Intune check-in
- Configure the following
- Open new tab in the browser and go to the Firefox Policy Template site:https://github.com/mozilla/policy-templates/releases
-
Under the Assets section, click policy_templates.zip to download the file. Note that the file name or version number may vary depending on the latest release available.

-
Extract the downloaded zip file.
-
Open the extracted folder, then navigate to policy_templates > windows (folder name may vary depending on the version).
-
Locate the firefox.admx file inside.

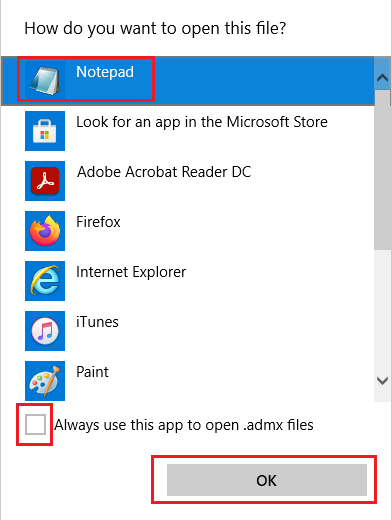
- Right-click on the file, firefox.admx. Select Open with, choose Notepad, and click OK. Ensure that “Always use this app to open…” is unchecked.
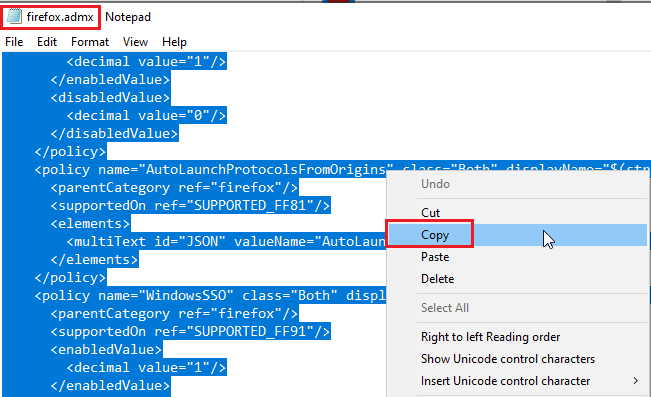
- Press Ctrl + A to select all text, then right-click and choose Copy. You will need this content later.
- Now return to Intune and create a new policy.
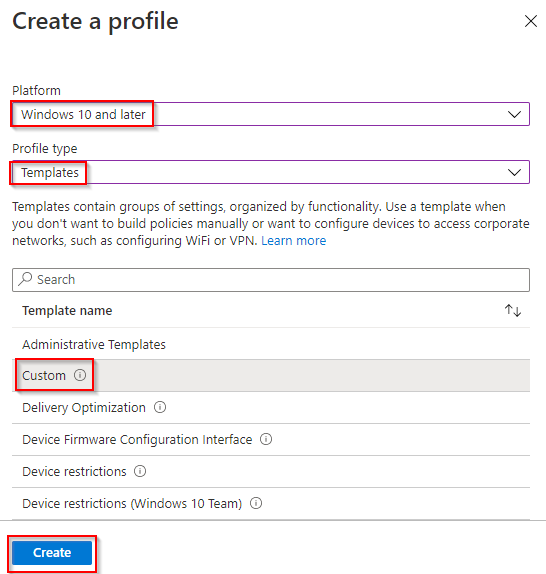
- Configure the following settings:
-
Platform: Windows 10 and later
-
Profile type: Templates
-
Template name: Custom
-
- Click Create.
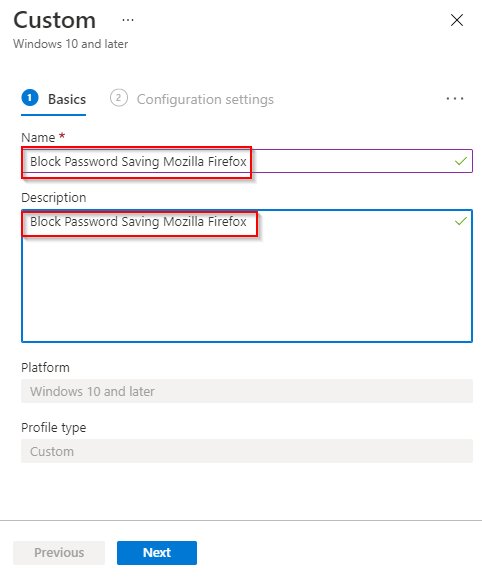
- Name the profile to Block Password Saving – Mozilla FireFox and click Next.
- In the Configuration settings section, click Add next to OMA-URI Settings.
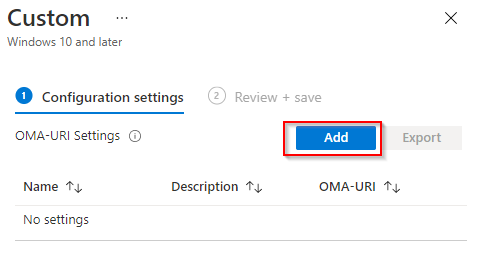
- Configure the following settings:
-
Name: Firefox ADMX
-
OMA-URI: Copy and paste the below URI:
./Device/Vendor/MSFT/Policy/ConfigOperations/ADMXInstall/Firefox/Policy/FirefoxAdmx -
Data type: Select String in the dropdown
-
Value: Paste the contents you copied from Step 7

-
- Click Save. Firefox ADMX is now added.
- click on Add again next to OMA-URI Settings.
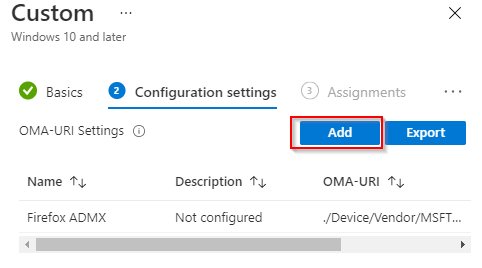
- Configure the following:
-
Name: PasswordManagerEnabled
-
OMA-URI:
./Device/Vendor/MSFT/Policy/Config/Firefox~Policy~firefox/PasswordManagerEnabled -
Data type: String
-
Value:
<disabled/> 
-
- Click Save.
- Add another OMA-URI Settings. Click Add.

- Configure the following:
-
Name: DisableFirefoxAccounts
-
OMA-URI:
./Device/Vendor/MSFT/Policy/Config/Firefox~Policy~firefox/DisableFirefoxAccounts -
Data type: String
-
Value:
<enabled/>
-
- Click Save.
- Click Add again

- Configure the following:
-
Name: OfferToSaveLogins
-
OMA-URI:
./Device/Vendor/MSFT/Policy/Config/Firefox~Policy~firefox/OfferToSaveLogins -
Data type: String
-
Value:
<disabled/>
-
- Click Save. Then, click Next.

- On the Assignments tab, Click on Add all users and Add all devices. Note: If you don’t want to deploy the policy to all users, select Add groups instead and assign it only to the preferred group.
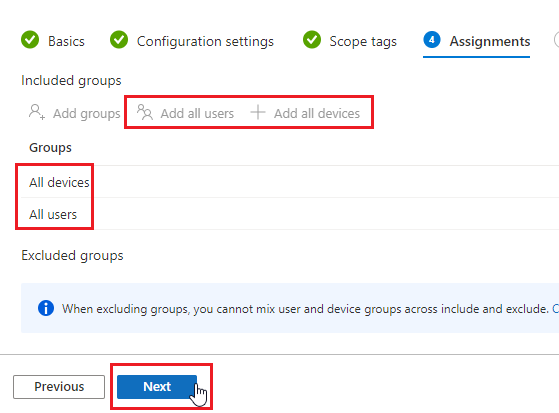
- Leave the Applicability Rules as Default, and click Next.

- Review all the settings and ensure that all Firefox configurations have been added correctly.

- Click Create
- The policy will be enforced on targeted devices/users at their next Intune check-in
