This article provides a contextual overview and implementation steps for setting policy guidelines around IT and internet usage within an accounting or bookkeeping firm. This process is designed to deploy a firmwide technology code of conduct that defines acceptable use and team member obligations with respect to client data privacy. Taking this step is a significant demonstration of risk management and liability limitation in the event a breach happens.
Why should my team share responsibility for client data security?
A team member’s actions during usage of company systems can have a severe impact on the firm’s privacy however it is the firm’s commercial obligation to set what ‘actions’ are and aren’t acceptable from a policy perspective. If you don’t define the rules of the game, you have no recourse if they’re broken.
Client data security is a people issue. Implementing world best cyber defence technology significantly contributes, but tech alone cannot protect your firm from accidental clicks or team members mistakenly breaching client data. Hackers don’t hack, they trick. Criminals are not technical geniuses, developing highly sophisticated technologies to breach your data stores. Criminals and fraudsters are focused on devising and executing strategies to trick your team members into divulging access to these systems. It’s an interesting one because most of us assume that cyber criminals are experts in technology which isn’t necessarily true. They’re experts in deception and as our defences get smarter, they’re continually evolving new ways to breach your firm’s perimeter via the ultimate wildcard within any business. People.
So what should I do to make everyone in my team responsible for client data privacy?
In a fast-paced firm, people are busy and if you attempted to use technology only to guarantee no breaches can occur, you’d quickly hit a point where productivity is impacted. We’ve seen firms attempt this, but we try to take a more realistic approach as we understand that any bottleneck to workflow is unacceptable within a busy firm.
The solution is a combination of education and compliance so that a firm can easily demonstrate due diligence and fairness in the event a team member does happen to make that costly mistake.
Answer these questions:
Q: Is your firm ok with remote team members accessing client data on their 16-year-old nephew’s computer rather than your company computer?
Q: Is your firm ok with team members installing unverified personal applications or browsing unsolicited personal websites?
Q: Is your firm ok with company computers being used by your team’s family members for non-work related tasks?
In most cases, the answer is a resounding no. However, if your firm isn’t setting the ‘rules of the game’ on the do’s and don’ts, you have no recourse or indemnity in the event of a breach that results from an error. No matter how obvious it seems.
Implementation the easy way
Here’s what you need to do to manage your risk and stay compliant around these events…
Step 1 – Provide access to cyber security training.
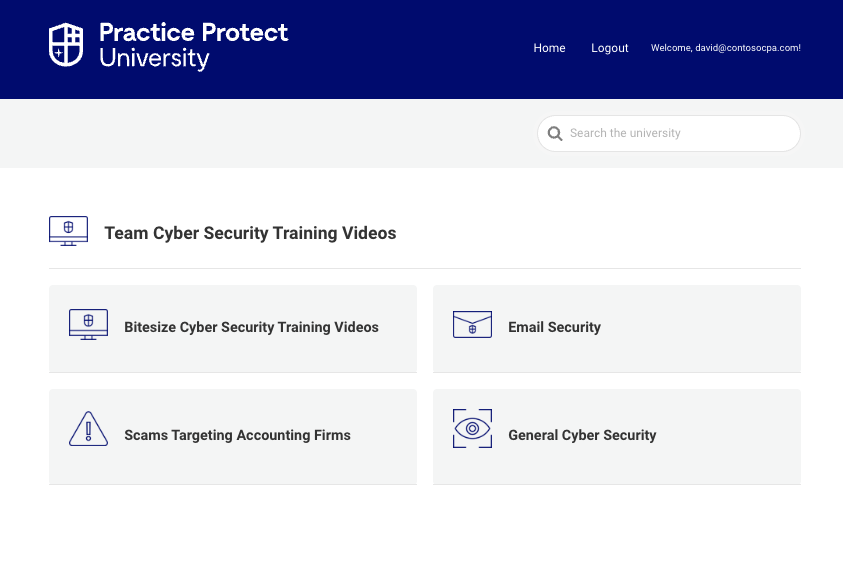
Firstly, you must provide your team with access and a strong recommendation to cyber security training that set the rules of the game. You can find suitable training in the Practice Protect University at Team Cyber Security Training Videos – Practice Protect University
Prioritise the Password Security and Email Security videos by mandating that your team set time aside to view these.
Step 2 – Get sign off from your team on their obligations to client data protection.
Ask your team to acknowledge that they understand the rules of the game in your firm when it comes to protecting your clients against cyber-crime. You can get this done the easy way utilising our IT and Internet usage policy document template.
Here’s the US Version – IT & Internet Usage Policy – USA
Here’s the AU Version – IT & Internet Usage Policy – AU
The hard work is done by our legal team however you will need to review the document to make sure it fits inside your firm. The hour of work you’ll need to invest is a once off.
While we, nor any cyber security company can 100% guarantee a riskless future, we can tell you that based on our experience at the coal face, having a reference to these two steps in the event of a breach goes a long way to ensuring your indemnification. Yes, there’s a lot more you can do but in terms of value for time, this is the number 1 risk mitigation measure you can implement in your firm.
For any assistance with this implementation feel free to reach out to your client success team! We would love to help you take this massive step towards responsible client data custodianship.
