Purpose
Federated identity with Practice Protect offers the best overall end user SSO experience in the Microsoft cloud and offers unique security options not available in standard deployments. Once Federation & Provisioning is in place all Office 365 Identities will be managed from Practice Protect and login at the Office 365 website is no longer possible.
Similar to pass-through authentication, user logon attempts are passed back to the Practice Protect farm to validate logins against your custom polices. Outlook/Skype For Business 2013 or later will leverage modern authentication to communicate with Practice Protect. Web browsers will get redirected to the Practice Project to complete their authentication. This lets us use what’s called SmartLinks technology to allow users to logon directly to SharePoint and other Office 365 Apps without entering a username or password.
We also have access to security features not available in other scenarios. We can enable client access filtering which lets us restrict access to Microsoft cloud services based on IP address (commonly used when we have hourly employees that shouldn’t be able to check email from home). We also provide multi-factor authentication.
Note: This guide ONLY applies to deployments running Active Directory Sync to Office 365 and Practice Protect. In addition, this applies to a domain level change.
Prerequisites
- Administrator Access to your Office 365 Account (Needed to Create Service Account – i.e. practiceprotect@emaildomain.onmicrosoft.com) You can follow the following guide Create Practice Protect Service Account.
- Register an Azure Application (Token-Authentication)
- Practice Protect Active Directory Connector installed and connected to the Local AD Server (Practice Protect Accounts are replicated from Local Active Directory)
- Active Directory Synced to Office 365 – On Premise
Instructions
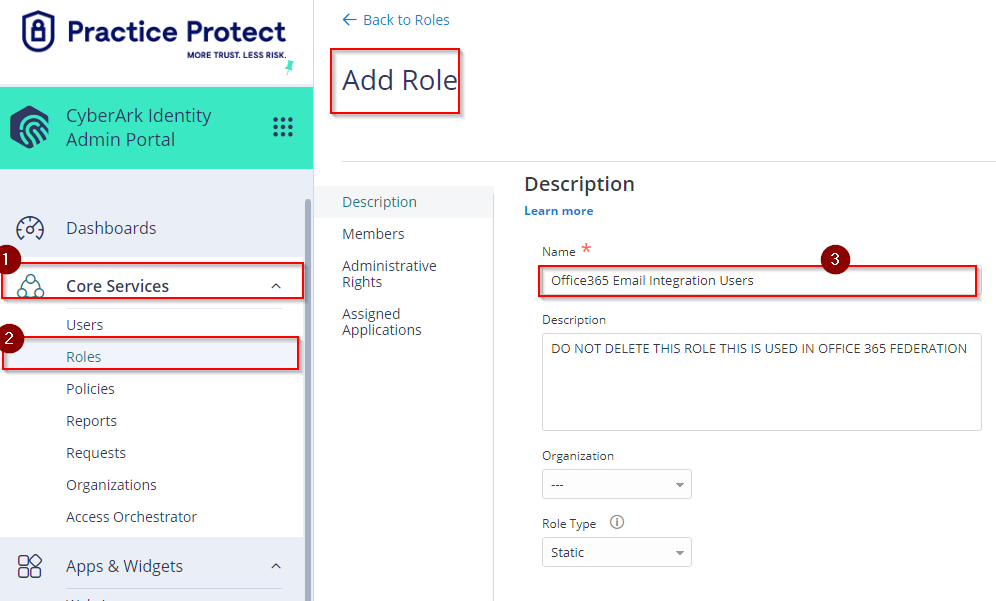
- Under Core Services Click on Roles –> Click on Add Role –> Type Office 365 Email Integration Users on the Name field, then Click Save.
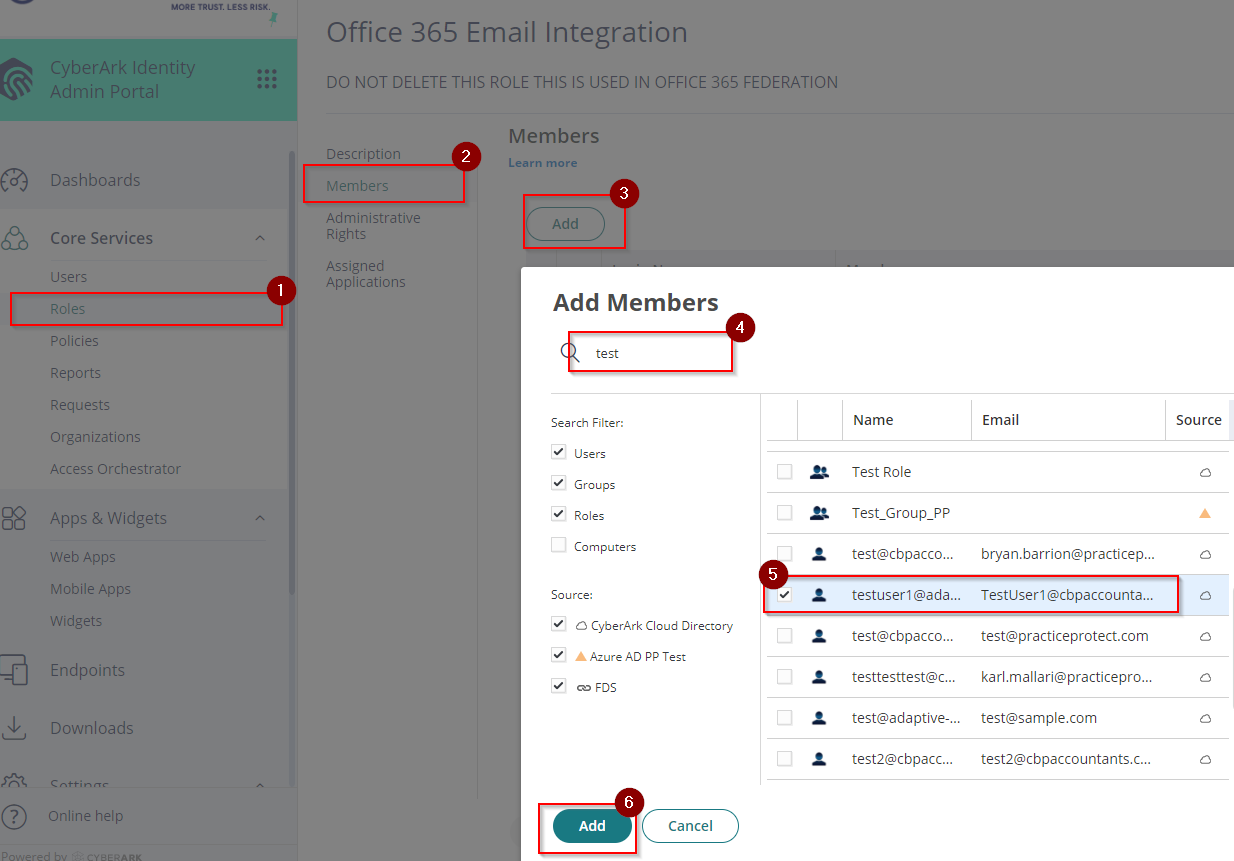
- Newly created Role (Office 365 Email Integration Users) should now show up on the list. Click on Office 365 Email Integration Users role –> Click Members –> Click Add –> On the search field type the Name of the user(s) –> Tick the box on the side of the Name then Click Add –> Click Save.
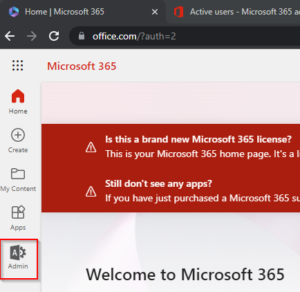
- Login to Office365 portal using the Office365 Service Account credential (Global Admin).
- Click on Admin to go to the Admin Center.
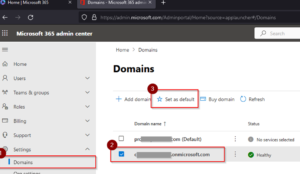
- On the Admin center, Click on Settings -> Click Domains -> On the Domain name select the Domain with .onmicrosoft.com then Click Set as default.
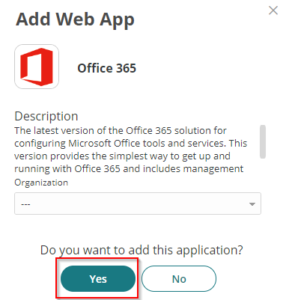
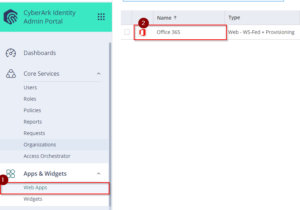
- Go back to the Practice Protect Admin Portal. Click on Apps –> Add WebApps –> Type Office 365 on the search field –> Select Office 365 (WS-Fed +Provisioning) –> Click Add

- On Add Web App page, click Yes.
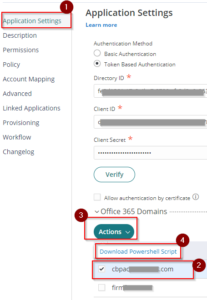
- On the Application Settings, select Token Based Authentication then enter the Directory ID, Client ID and Client Secret that was registered in AzureAD.
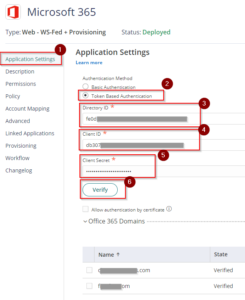
- Click Verify. If the credentials are correctly set, this will show all available email domain that can be federated.
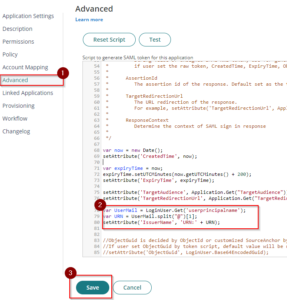
- Under the Advanced settings, paste the script below after line 76. Then Save. This configuration sets the Issuer URI/URN for the SAML token response and identifies the domain that the token is associated with.
var UserMail = LoginUser.Get('userprincipalname');
var URN = UserMail.split("@")[1];
setAttribute('IssuerName', 'URN:' + URN); - This should complete the configuration of the integration/federation. Provisioning shall be skipped as Office365 syncs to Local AD.
Enabling Office365 Email Integration/Federation
- Return to the Office365 tile/app in the Admin Portal.
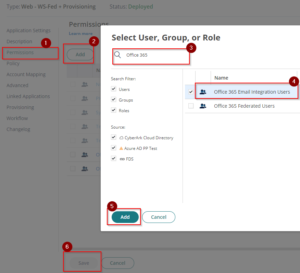
- On Permissions, Add the role which contains the user for email integration (i.e. Office 365 Email Integration Users) and click Save to apply. This should display the app on their user portal and can be used once federated.
- Return to the Application Settings and then on Office 365 Domains section, tick the box beside the Domain(s) Name (i.e. youremaildomain.com) –> Click Actions –> Select Download Powershell Script and save the downloaded file as it will be used in the following steps to federate.
- Go to the downloaded file from Step 3 and Right Click –> click Run with PowerShell. This will prompt to login and authenticate. Use the Office365 Admin Account.
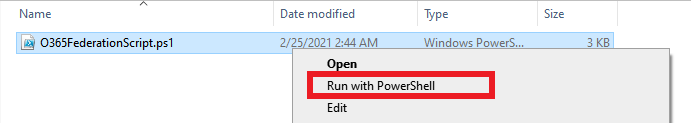
- With the prompt “What Action Would You Like To Do?” press F. The script will run and federate your domain.

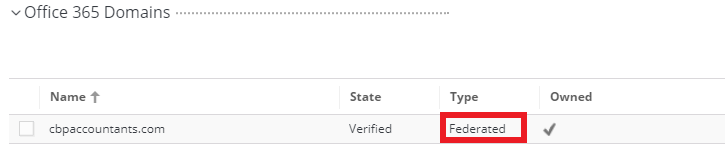
- Once the script is completed, Go back to Office365 web app settings in Practice Protect. On the Office 365 Domains section check the Type of the domain (i.e. cbpaccountant.com) , It should now be Federated. (Optional) Refresh the page to show latest state and type.
- (Optional) Repeat step 3 to 6 to federate other domains.
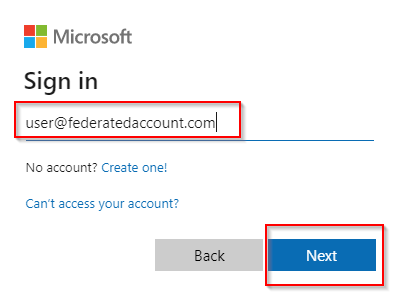
- Test federation if it is working by signing in to a user account in Office 365, Once you type the user name/email address the page will redirect to Practice Protect.
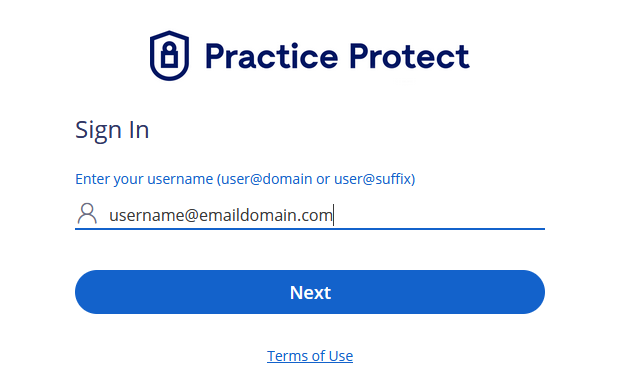
- To authenticate and access, login using an active Practice Protect account credentials.
- Enable ADAL/Modern Authentication in Office 365 – This is to apply Practice Protect MFA (Multi-Factor Authentication) and security policies as Basic Authentication doesn’t enforce MFA and also applies if using Outlook 2013 or later clients. See here for more information.
- If you have your Office 365 Email configured on Outlook or Mobile you will now be prompted to login with your Practice Protect Account.
- (Recommended) Post federation Practice Protect recommends disabling legacy protocols/basic authentication (i.e. POP, IMAP, Auth SMTP) in Office365. Please see following guide.